Most people think scheduling privacy means hiding who voted for which date, but that's only half the story. True anonymous scheduling protects not just your preferences but your identity, metadata, and participation patterns from being tracked or linked back to you. As group event planning becomes more complex and privacy concerns grow, understanding how anonymous scheduling works can transform the way you coordinate corporate retreats, family gatherings, and community activities. This guide explains what anonymous scheduling really means, how it differs from standard tools, and why it matters for your next group event.
Table of Contents
- Key takeaways
- Understanding anonymous scheduling: Definition and core principles
- How anonymous scheduling works in practice: Technologies and protocols
- Benefits and challenges of anonymous scheduling for group events
- Implementing anonymous scheduling: Practical tips and tools for event planners
- Discover privacy-focused scheduling solutions with WhenNOT
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Definition and scope | Anonymous scheduling aims to coordinate events without exposing participants' identity or their preferences. |
| End to end encryption | End to end encryption prevents others including the service from reading scheduling data. |
| Blinded queries | Blinded queries allow matching dates without revealing who submitted which responses. |
| Metadata leakage risk | Standard polls can hide votes but still leak IPs, timestamps, and activity patterns. |
| Decentralized privacy advantage | Decentralized protocols like OpenSlots provide stronger privacy with end to end encryption and no central data vault. |
Understanding anonymous scheduling: Definition and core principles
Anonymous scheduling arranges events without identifying participants or linking their preferences to personal information. Unlike conventional scheduling apps that collect names, email addresses, and timestamps, anonymous systems eliminate or encrypt identifying data at every step. The goal is simple: let people coordinate group events while preserving their privacy from both the platform operator and other participants.
Three foundational principles define genuine anonymous scheduling. First, no peer-reviewed paper defines 'anonymous scheduling' directly, but cryptography research on anonymous communication provides the blueprint. No trusted third party should access unencrypted participant data. Second, end-to-end encryption protects all communications so only intended recipients can read scheduling information. Third, blinded queries allow the system to match available dates without learning who submitted which preferences.
Most standard scheduling apps fail these tests. They may claim vote anonymity, meaning your colleagues can't see who picked Tuesday versus Wednesday, but the platform itself collects extensive metadata. Your IP address, device fingerprint, access timestamps, and participation patterns create a detailed profile. That metadata can reveal your identity through traffic analysis or data breaches, even when your name isn't directly attached to your vote.
Designing truly anonymous scheduling systems presents technical challenges. Metadata leaks through multiple channels:
- Network traffic patterns reveal when and how often you access the scheduling page
- Device identifiers link multiple sessions to the same person
- Timing correlations connect your responses with other activities
- Server logs capture IP addresses and user agent strings
These challenges matter most for groups needing strong privacy protections. Corporate retreat planners handling sensitive executive schedules, community organizers coordinating activism, and family event coordinators protecting children's information all benefit from anonymous approaches. Privacy in scheduling drives event success by building participant trust and reducing coordination friction.
How anonymous scheduling works in practice: Technologies and protocols
Two distinct technological approaches enable anonymous scheduling: centralized platforms with privacy features and fully decentralized protocols. Each offers different privacy guarantees and usability tradeoffs.
Salesforce Scheduler uses screen flows, scheduling policies, and guest user profiles for anonymous booking without requiring login. The system creates a public scheduling page accessible to anyone with the link. Visitors select appointment slots through a guided flow that assigns resources automatically based on availability rules. No account creation or personal information entry is required. The hierarchy works through scheduling policies that define which resources (meeting rooms, team members, equipment) match specific appointment types, then applies those rules when anonymous users request bookings.
This centralized approach protects identity from other participants but not from the platform operator. Salesforce still collects session data, IP addresses, and booking patterns for system administration and analytics. For many business use cases, this level of privacy suffices because the organization running the scheduler already has legitimate access to participant information.
OpenSlots protocol offers decentralized anonymous scheduling with end-to-end encryption and blinded indexing. Built on the Nostr protocol, it uses NIP-44 encryption to protect all scheduling messages. Event organizers create scheduling requests as encrypted Nostr events. Potential participants receive these requests through relay servers that cannot read the encrypted content. When someone marks their unavailable dates, the response gets encrypted before transmission, and zero-knowledge URL fragments ensure even the relay servers cannot link responses to individuals.
The decentralized model eliminates the trusted third party entirely. No central server sees unencrypted scheduling data. Relay servers only forward encrypted messages without learning their contents or correlating senders with recipients. This architecture provides stronger privacy guarantees but requires participants to manage cryptographic keys and understand decentralized systems.
| Feature | Salesforce Scheduler | OpenSlots Protocol |
|---|---|---|
| Architecture | Centralized platform | Decentralized relays |
| Encryption | Transport layer (HTTPS) | End-to-end (NIP-44) |
| Identity Protection | From other participants | From all parties |
| Login Requirement | None (guest access) | None (key-based) |
| Metadata Protection | Limited (server logs exist) | Strong (blinded indexing) |
| Setup Complexity | Low (admin configures) | Medium (key management) |
Pro Tip: Using Tor or secure networks when accessing any scheduling tool reduces metadata leakage risks even further by hiding your IP address and routing traffic through multiple nodes.
Both approaches support decentralized scheduling for event planning differently. Salesforce decentralizes access (anyone with a link can book) while centralizing data storage. OpenSlots decentralizes both access and data storage across relay servers. Your choice depends on whether you need protection from the platform operator itself or just from other participants. For practical examples of scheduling apps implementing these principles, consider how each balances privacy with ease of use.
Benefits and challenges of anonymous scheduling for group events
Anonymous scheduling delivers four major advantages for event organizers and participants. First, enhanced privacy protection builds trust. When participants know their identity and preferences remain confidential, they respond more honestly about availability. This matters especially for sensitive events where revealing attendance itself carries risks, like community organizing meetings or confidential business retreats.

Second, anonymous systems reduce scheduling conflicts by encouraging participation. People who might skip traditional polls due to privacy concerns engage with anonymous tools. Higher response rates give organizers better data for finding optimal dates. Third, compliance with data protection regulations becomes simpler. True anonymity requires no TTP, E2EE, and blinded queries, which means less personal data collection and fewer regulatory obligations under laws like GDPR or CCPA.
Fourth, anonymous scheduling can streamline coordination by removing authentication friction. No login requirements mean participants access scheduling pages instantly without password resets or account creation delays. This speed advantage compounds for large groups where even small friction points multiply across dozens of participants.
However, three significant challenges complicate anonymous scheduling adoption. Residual metadata leakage remains the primary technical limitation. Even with strong encryption, network traffic analysis can reveal participation patterns. Your internet service provider sees when you access a scheduling page. Correlation attacks might link your encrypted responses to your identity by timing or network behavior. IP address exposure tells observers your approximate location and can fingerprint your device across multiple sessions.
Technology complexity creates the second barrier. Decentralized protocols require participants to understand key management and secure communication channels. While centralized anonymous schedulers simplify the user experience, they reintroduce trust assumptions about the platform operator. Striking the right balance between security and usability challenges even experienced developers.
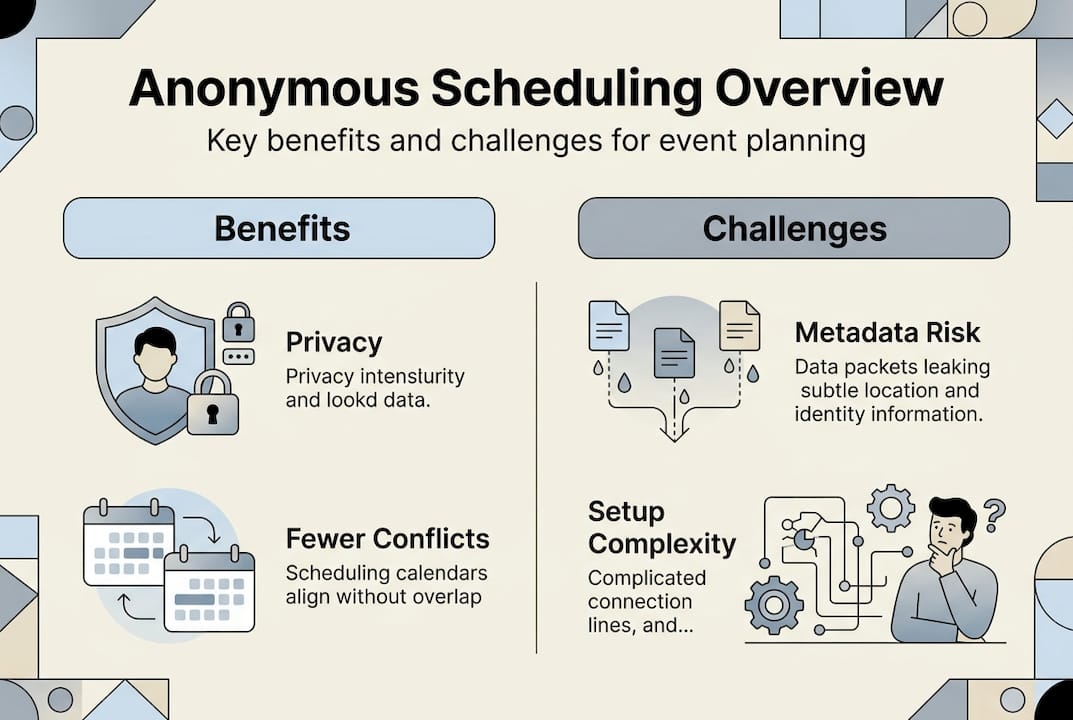
User experience hurdles form the third challenge. Participants accustomed to traditional scheduling tools may find anonymous systems confusing or suspicious. Why does this poll not ask for my name? Is this legitimate? Education and clear communication about privacy protections become essential for adoption.
Mitigation strategies address these challenges effectively. Using Tor browser or VPN services masks IP addresses and prevents traffic analysis. Accessing scheduling tools only through secure networks reduces metadata exposure. Educating participants about how anonymous systems protect them increases trust and adoption rates.
Anonymous scheduling proves especially advantageous in specific scenarios:
- Sensitive community meetings where attendance itself might be monitored
- Corporate retreats involving confidential strategy discussions
- Family events coordinating across households with complex privacy needs
- Group travel planning where participants prefer not to reveal their availability to everyone
- Healthcare appointment scheduling protecting patient confidentiality
Pro Tip: Educate participants early about privacy protections to increase adoption. Send a brief explanation with the scheduling link describing how their information stays confidential and why anonymous scheduling benefits everyone.
Privacy in scheduling for faster multi-day events becomes particularly valuable when coordinating complex itineraries. Efficient group scheduling workflows benefit from anonymous approaches by removing authentication barriers and encouraging honest availability reporting.
Implementing anonymous scheduling: Practical tips and tools for event planners
Adopting anonymous scheduling for your group events requires methodical planning and tool selection. Follow this step-by-step checklist to implement privacy-focused coordination:
- Assess your privacy requirements by identifying what information needs protection (identity, preferences, participation patterns)
- Evaluate whether you need protection from the platform operator or just from other participants
- Choose between centralized anonymous tools (easier setup) or decentralized protocols (stronger privacy)
- Test the selected tool with a small group before rolling out to your full event participant list
- Prepare clear communication explaining how the anonymous system protects participant privacy
- Distribute the scheduling link through secure channels to prevent unauthorized access
- Monitor response rates and follow up with non-responders using privacy-preserving methods
- Review collected availability data without attempting to de-anonymize participants
- Communicate the selected dates to all participants using the same secure channels
Comparing popular scheduling tools reveals significant differences in privacy features:
| Tool | Anonymous Booking | End-to-End Encryption | No Login Required | Metadata Protection | Best For |
|---|---|---|---|---|---|
| OpenSlots | Yes | Yes | Yes | Strong | Maximum privacy needs |
| Salesforce Scheduler | Yes | No | Yes | Moderate | Business events |
| Doodle Poll | No | No | Optional | Weak | Simple availability checks |
| Calendly | No | No | No | Weak | One-on-one appointments |
| WhenNOT | Partial | No | Yes | Moderate | Multi-day group events |
Communicating privacy benefits to participants increases trust and participation rates. When sending your scheduling link, include a brief note like: "This anonymous scheduling tool protects your privacy by not collecting names or email addresses. Only the event organizer sees the final availability summary, and your individual responses remain confidential." This transparency builds confidence and encourages honest availability reporting.
Pro Tip: Use tools that support no-login bookings and encrypted communications for best privacy outcomes. Prioritize platforms that clearly document their data handling practices and offer verifiable privacy guarantees.
Testing workflows before major event planning identifies gaps and improves user experience. Create a trial event with colleagues, run through the entire scheduling process, and gather feedback about confusing steps or unclear instructions. Common issues include:
- Participants unsure whether they successfully submitted their availability
- Confusion about how to access the scheduling page on mobile devices
- Uncertainty about whether they can change their responses after initial submission
- Questions about how their privacy is actually protected
Address these concerns in your communication materials and tool selection. Ways to avoid scheduling conflicts easily include choosing platforms with clear user interfaces and confirmation messages. For comprehensive guidance, review best group scheduling tools 2025 comparison to understand how different platforms balance privacy with functionality.
Discover privacy-focused scheduling solutions with WhenNOT
WhenNOT offers a practical approach to privacy-conscious scheduling by eliminating account requirements and minimizing data collection. The platform's inverse scheduling method asks participants when they are not available rather than requiring them to share their full calendars. This approach naturally protects privacy by collecting less information while still enabling efficient date coordination.
Participants access scheduling pages through simple links without creating accounts or providing email addresses. The platform visualizes everyone's unavailable dates concurrently, helping organizers identify optimal dates quickly while maintaining participant confidentiality. For group events requiring both privacy protection and ease of use, WhenNOT's privacy-focused scheduling platform provides a balanced solution that streamlines coordination without compromising data security.
Frequently asked questions
What does 'anonymous scheduling' mean in everyday terms?
Anonymous scheduling lets you coordinate group events without revealing who you are or when you're available to other participants or the platform itself. Instead of entering your name and email, you simply mark dates that don't work for you, and the system matches everyone's availability without tracking your identity. It's like voting in a secret ballot where even the vote counters can't connect your vote to your identity.
How does anonymous scheduling protect my identity compared to standard systems?
Standard scheduling tools collect your name, email, IP address, and timestamps, creating a detailed profile even when they hide your vote from other participants. Anonymous scheduling uses encryption and blinded indexing so the platform cannot link your responses to your identity. The strongest systems eliminate trusted third parties entirely, meaning no one, not even the service operator, can see who submitted which availability preferences.
Can I use anonymous scheduling for any type of group event?
Anonymous scheduling works well for most group events including family gatherings, corporate retreats, community meetings, and group travel planning. It's especially valuable when privacy concerns might discourage participation or when coordinating sensitive events. However, events requiring payment processing or legal agreements may need some identity verification, which limits full anonymity.
Are there limitations to anonymity I should be aware of?
Yes, residual metadata can leak through network traffic patterns, IP addresses, and timing correlations even with strong encryption. Your internet provider sees when you access scheduling pages, and sophisticated attackers might link your responses to your identity through traffic analysis. Using Tor or VPN services mitigates these risks. Additionally, very small groups make it easier to guess who submitted which responses through process of elimination.
What tools exist today to facilitate anonymous scheduling?
OpenSlots provides decentralized anonymous scheduling with end-to-end encryption and no central authority. Salesforce Scheduler offers anonymous booking through guest access without login requirements, though the platform still collects some metadata. WhenNOT simplifies group coordination with no-account scheduling that minimizes data collection. Each tool balances privacy protection with ease of use differently, so choose based on your specific privacy requirements and technical comfort level.
