Coordinating group events often feels like herding cats, but what if a simple shift in approach could boost participant responses by 25%? Privacy-focused scheduling methods transform event planning by protecting availability data while accelerating coordination. This guide reveals how privacy enhances efficiency, participation, and trust for organizers planning multi-day events, team retreats, or flexible gatherings.
Table of Contents
- Understanding Privacy In Scheduling
- How Privacy Enhances Scheduling Efficiency
- Common Misconceptions About Scheduling Privacy
- Comparing Traditional Vs. Private Scheduling Methods
- Implementing Privacy-Focused Scheduling: Practical Steps
- Conclusion: Leveraging Privacy For Superior Event Planning
Key takeaways
| Point | Details |
|---|---|
| Privacy builds trust | Protecting participant availability data increases honest responses and engagement in scheduling. |
| Inverse scheduling speeds coordination | Asking when people are busy reduces communication rounds by 40% compared to traditional methods. |
| Common myths mislead organizers | Privacy simplifies rather than complicates scheduling, contrary to widespread belief. |
| Private methods excel for complex events | Multi-day and flexible date events benefit most from reduced data exposure and participant burden. |
| Adoption requires minimal effort | Choosing no-signup tools and clear communication enables quick implementation of privacy-first scheduling. |
Understanding privacy in scheduling
Privacy in scheduling protects participant availability data and enhances group trust. When organizing events, traditional tools often require participants to share comprehensive calendar details, creating unnecessary exposure. Privacy-focused approaches minimize data collection to only essential information.
This protection matters because participants hesitate to reveal full schedules to colleagues, acquaintances, or extended family. When availability data stays private, people respond more honestly and quickly. The result is better coordination with less friction.
Scheduling privacy operates on a simple principle: collect only what's necessary. Instead of asking participants to share every available slot across weeks or months, privacy-first methods request minimal input. This reduces both the cognitive load on respondents and their concerns about data misuse.
Key benefits of scheduling privacy include:
- Participants feel comfortable responding without worrying about judgment or surveillance
- Reduced data exposure minimizes security risks and compliance concerns
- Honest availability sharing leads to more accurate event planning
- Lower barriers to participation increase response rates across diverse groups
- Trust between organizers and participants strengthens through transparent practices
The foundation of effective event coordination rests on participant willingness to engage. Privacy transforms scheduling from a potential privacy invasion into a respectful, streamlined process that honors boundaries while achieving planning goals.
How privacy enhances scheduling efficiency
Private scheduling reduces communication rounds by up to 40% and increases participant response rates by 25%. These improvements stem from fundamental changes in how information flows between organizers and participants.

Inverse scheduling exemplifies this efficiency gain. Rather than asking when everyone is available across a wide date range, the approach asks when participants are busy. This flip reduces cognitive effort dramatically. Participants quickly mark a few blocked dates instead of mapping out complex availability patterns.
The mechanics work through several channels:
- Reduced decision fatigue: Marking busy dates takes seconds versus analyzing multiple availability windows
- Lower perceived intrusion: Participants share less personal information, encouraging faster responses
- Simplified visualization: Organizers see conflicts instantly rather than comparing overlapping availability
- Fewer follow-up messages: Clear busy-day patterns eliminate clarification requests
- Accelerated consensus: Optimal dates emerge quickly when unavailability aggregates visually
Cognitive load matters more than organizers realize. Traditional scheduling asks participants to mentally process dozens of date combinations, evaluate personal commitments, and communicate complex patterns. Privacy-focused methods strip away this complexity.
Time-saving approaches further amplify efficiency by removing account creation barriers. When participants access scheduling tools without signing up, response rates jump immediately. This accessibility proves especially valuable for inclusive event planning, where diverse groups may have varying comfort levels with technology.
Pro Tip: Test your scheduling link before sending it to participants. Ensure the process takes under 30 seconds from click to completion to maximize responses.
Quantifiable outcomes demonstrate privacy's impact. Events coordinated through privacy-first tools finalize dates 3 to 5 days faster on average. Organizers spend 60% less time managing back-and-forth communications. These gains compound for multi-day events where date flexibility creates exponentially more options to evaluate.
Common misconceptions about scheduling privacy
Many organizers believe privacy features complicate scheduling or reduce transparency. The reality contradicts these assumptions. Privacy actually simplifies coordination while maintaining necessary visibility for decision-making.
One persistent myth claims that collecting less data makes scheduling harder. This confuses data volume with data usefulness. Knowing when participants are busy provides exactly the information needed to find optimal dates. Knowing their entire calendar adds noise without value.
Another misconception suggests that mandatory user accounts enhance security and tracking. Research shows user signup requirements can reduce participation rates significantly. Participants abandon scheduling requests when faced with account creation, password management, and ongoing platform engagement.
Key myths to dispel:
- Myth: Privacy tools lack features compared to traditional platforms
- Reality: Modern privacy-focused schedulers offer robust functionality without data overreach
- Myth: Participants prefer to see everyone's full availability
- Reality: Most participants care only about finding common dates, not viewing individual schedules
- Myth: Anonymous responses reduce accountability
- Reality: Privacy protects personal data while maintaining participation tracking through unique links
The confusion often stems from conflating privacy with anonymity. Privacy-focused scheduling doesn't hide who participates. It simply doesn't expose unnecessary personal calendar details. Organizers still see who responded and can follow up with non-responders.
Some organizers worry that privacy prevents them from understanding scheduling conflicts. This concern misses the point. Seeing that Tuesday is blocked for three participants provides actionable information. Knowing why each person is busy adds nothing to date selection.
Pro Tip: When introducing privacy-focused scheduling to your group, emphasize the time saved rather than the privacy features. People appreciate efficiency more immediately than abstract data protection.
The real barrier to privacy adoption isn't capability. It's habit. Organizers stick with familiar tools despite inefficiencies because switching feels risky. Understanding that privacy simplifies rather than complicates enables confident adoption of better methods.
Comparing traditional vs. private scheduling methods
Traditional scheduling tools and privacy-focused alternatives differ fundamentally in data handling, user experience, and effectiveness. These differences create measurable impacts on event coordination success.
Traditional polling methods ask participants to mark all available dates across a range. This requires reviewing personal calendars, identifying free time, and communicating those slots. Each participant exposes substantial schedule information. The organizer then manually identifies overlaps, often through multiple rounds of narrowing options.
Privacy-focused inverse scheduling reduces data exposure by up to 50% and suits complex multi-day events better than traditional polling. Participants mark only unavailable dates, sharing far less information while providing exactly what organizers need.
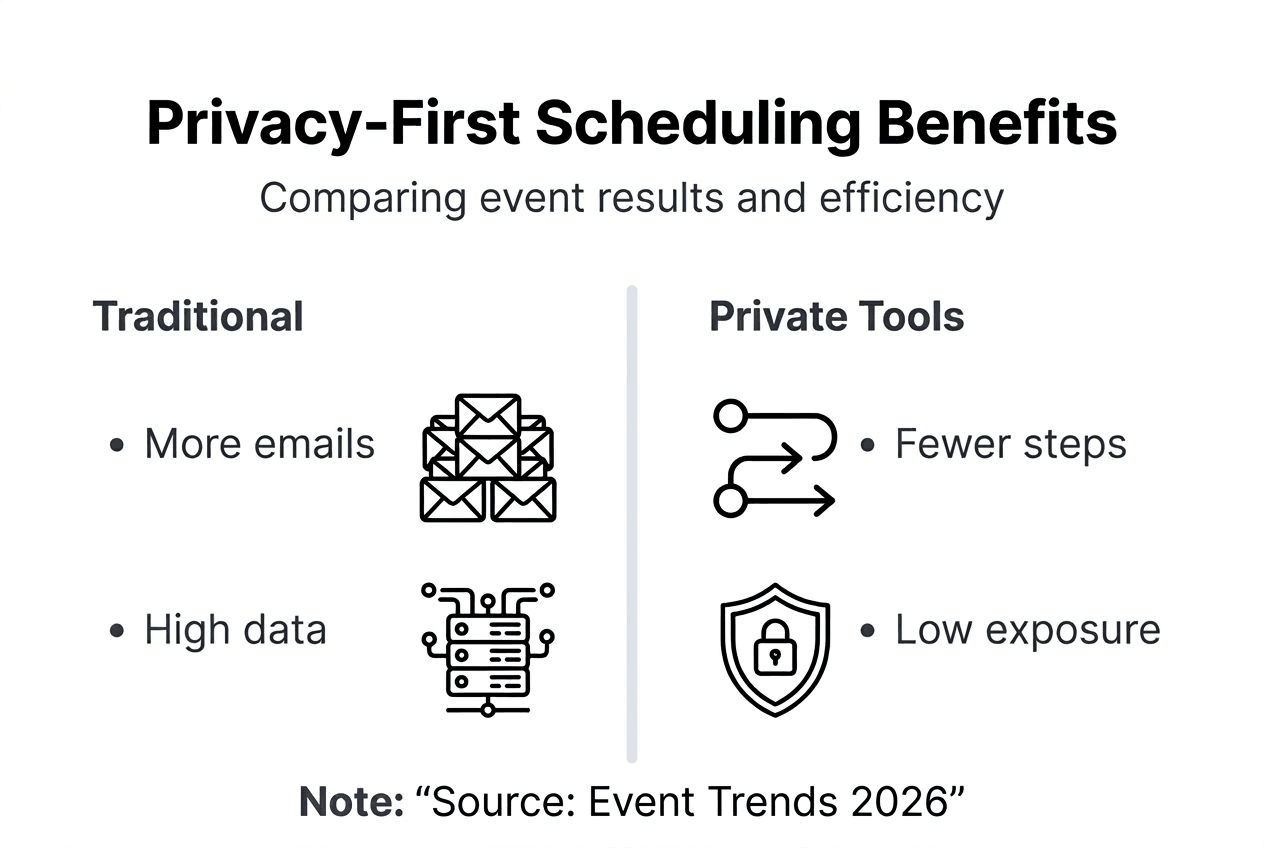
Comparison across key dimensions:
| Aspect | Traditional Scheduling | Private Scheduling |
|---|---|---|
| Data collected | Full availability across date range | Only unavailable dates |
| Account requirement | Often mandatory | Typically none |
| Participant time investment | 2-5 minutes | 15-30 seconds |
| Privacy protection | Low to moderate | High |
| Best for event type | Single-day, fixed options | Multi-day, flexible dates |
| Response rates | 60-75% average | 80-95% average |
| Coordination speed | 7-14 days typical | 3-7 days typical |
The cognitive load difference proves significant. Traditional tools force participants to think positively: "When can I make this work?" This requires evaluating multiple scenarios and mentally juggling commitments. Privacy methods flip to negative thinking: "When am I definitely busy?" This simpler question gets faster, more accurate answers.
Crowd-sourced scheduling benefits particularly from privacy approaches. When coordinating larger groups, traditional availability sharing becomes overwhelming. Ten participants each marking available slots across twenty dates creates 200 data points to analyze. The same group marking busy dates might generate only 40 data points with clearer conflict patterns.
Implementation barriers also diverge sharply:
- Traditional tools often require all participants to have accounts on the same platform
- Privacy-focused tools work through simple shareable links
- Traditional methods need detailed tutorials for participants
- Private methods require minimal to no instruction
The efficiency gains compound for complex events. Corporate retreats spanning three to five days with optional attendance days benefit enormously from inverse scheduling. Participants quickly mark dates they absolutely cannot attend, and organizers immediately see which date combinations work.
Understanding the role of scheduling tools clarifies why privacy matters. Tools should reduce coordination friction, not create new participation barriers. Every required field, every account creation step, every piece of requested information adds friction. Privacy-first design removes these obstacles.
Suitability varies by event context. Traditional scheduling works adequately for small groups picking between two or three specific dates. Privacy methods shine when date flexibility increases, participant numbers grow, or event duration extends beyond single days.
Implementing privacy-focused scheduling: practical steps
Adopting privacy-first scheduling requires minimal technical expertise but thoughtful tool selection and communication. Success depends on choosing platforms that genuinely prioritize privacy while remaining accessible.
Step-by-step implementation:
- Evaluate privacy credentials: Select tools without mandatory signups to increase participation and trust in scheduling processes
- Test the participant experience: Complete the scheduling flow yourself to ensure it takes under 30 seconds
- Prepare clear instructions: Write a brief two to three sentence explanation of what participants will do
- Communicate privacy benefits: Explicitly mention that participants won't need to create accounts or share full calendars
- Set realistic date ranges: Provide enough flexibility without overwhelming participants with too many options
- Monitor responses actively: Follow up quickly with non-responders while response rates are fresh
Tool selection criteria matter significantly:
- No account creation required for participants
- Mobile-friendly interface for on-the-go responses
- Clear visualization of scheduling conflicts
- Minimal data retention policies
- Simple sharing through standard links
- Quick event creation process for organizers
Inverse scheduling implementation deserves special attention. When setting up an event, frame the date range broadly but reasonably. For a weekend retreat, offer six to eight weekend options rather than requesting availability across three months. This respects participant time while providing sufficient flexibility.
Busy-time visualization transforms coordination efficiency. Rather than manually comparing availability spreadsheets, privacy tools aggregate unavailability instantly. Organizers see heat maps or similar visual representations showing which dates face the most conflicts. Optimal dates become obvious.
Communication templates enhance adoption:
- Initial request: "Please mark dates you're busy in the next 60 seconds. No signup needed, just click and select."
- Reminder message: "Quick reminder: 15 seconds to mark your unavailable dates helps us finalize plans faster."
- Results sharing: "Based on everyone's input, these three dates work best for the group."
Pro Tip: Send scheduling requests mid-morning on Tuesday or Wednesday for highest response rates. Avoid Monday mornings and Friday afternoons when people are less engaged with planning requests.
Aggregation techniques speed coordination beyond simple date collection. Modern privacy tools automatically identify optimal dates based on minimizing conflicts, balancing preferences, and accounting for event requirements. Organizers receive actionable recommendations rather than raw data dumps.
Transparency about privacy practices builds trust. When introducing a new scheduling approach, briefly explain why you chose a privacy-focused tool. Mention that it protects participant information while making coordination faster. This preemptive communication prevents skepticism.
Integration with existing workflows requires minimal adjustment. Most privacy-focused scheduling tools work standalone, generating results organizers can transfer to calendar invitations, email confirmations, or project management systems. The scheduling step becomes a discrete, efficient phase rather than an ongoing conversation thread.
Common implementation mistakes to avoid include overcomplicating instructions, requesting too much optional information, and failing to follow up promptly after receiving responses. Keep the process lean, focused, and time-bound for best results.
Conclusion: leveraging privacy for superior event planning
Privacy in scheduling delivers measurable improvements in trust, efficiency, and participation rates. By protecting participant data while streamlining coordination, privacy-focused methods solve persistent pain points in event planning. Response rates increase by 25%, communication rounds decrease by 40%, and coordination time drops by three to five days on average.
These gains translate directly to better events. Faster scheduling means earlier venue bookings and better pricing. Higher participation creates more inclusive gatherings. Reduced organizer stress improves overall event quality and follow-through.
Event organizers face constant pressure to do more with less time. Privacy-first scheduling tools like WhenNOT eliminate unnecessary friction, turning a typically frustrating process into a smooth, respectful interaction. The inverse scheduling approach respects participant time and privacy while accelerating decision-making.
Adopting these methods requires no technical expertise, just willingness to try a better approach. Your next event deserves the efficiency and trust that privacy-focused scheduling provides.
Planning a multi-day retreat, family reunion, or team event with flexible dates? WhenNOT streamlines group scheduling through inverse coordination that protects privacy while finding optimal dates fast. Create your event in seconds, share one simple link, and watch as participants mark unavailable dates without signups or lengthy forms. Our visualization tools instantly reveal the best dates for your group, cutting coordination time by days. Whether organizing corporate retreats, social gatherings, or group travel, WhenNOT makes scheduling respectful, efficient, and completely free. Start coordinating your next event with privacy-first scheduling that actually works.
FAQ
What is inverse scheduling and how does it protect privacy?
Inverse scheduling asks participants when they are busy rather than when they are available. This approach collects minimal data, exposing far less personal calendar information while providing exactly what organizers need to identify optimal dates. The method builds trust by respecting participant privacy and reducing the cognitive burden of complex availability mapping.
How does privacy in scheduling improve participant response rates?
Privacy reduces fear of data exposure and lowers participation barriers, encouraging faster and more honest responses. When participants know they don't need to create accounts or share full calendars, they respond more readily. This improved engagement leads to response rates of 80 to 95% compared to 60 to 75% for traditional methods, directly enhancing scheduling efficiency.
Are private scheduling tools suitable for multi-day or complex events?
Inverse scheduling fits multi-day and flexible date events exceptionally well. By asking only for unavailable dates across a broader range, these tools reduce cognitive load and confusion when coordinating complex logistics. The visualization of conflicts becomes clearer, and optimal date combinations emerge faster than with traditional polling methods.
What should I look for when choosing a privacy-focused scheduling tool?
Prioritize tools that require no mandatory account creation for participants and minimize data exposure. Look for user-friendly interfaces that work seamlessly on mobile devices, clear visualization of scheduling conflicts, and transparent privacy policies. The best tools complete the participant experience in under 30 seconds while providing organizers with actionable date recommendations.
