Planning a multi-day retreat? Your scheduling tool might be broadcasting participants' personal routines to everyone. Traditional event coordination platforms expose detailed availability patterns, creating privacy risks that most coordinators overlook. This exposure doesn't just threaten data security, it slows your entire planning process by making participants hesitant to share accurate schedules. Understanding privacy-first scheduling methods transforms event planning by protecting participant data while accelerating consensus, cutting scheduling time by up to 40%.
Table of Contents
- Understanding Privacy In Multi-Day Group Scheduling
- Common Privacy Risks In Traditional Scheduling Tools
- Inverse Scheduling: A Privacy-First Approach
- Privacy Compliance And Regulatory Considerations
- Technical Solutions For Enhancing Scheduling Privacy
- Practical Advice For Event Coordinators To Safeguard Privacy
- Common Misconceptions About Privacy In Scheduling
- Summary And Bridging Privacy To Efficient Multi-Day Event Scheduling
- Explore Privacy-First Scheduling Tools For Your Next Event
Key Takeaways
| Point | Details |
|---|---|
| Privacy risks reduce participation | Exposed availability data discourages accurate schedule sharing, causing delays |
| Inverse scheduling minimizes exposure | Asking when participants are busy instead of available protects sensitive information |
| Compliance is mandatory | GDPR and similar regulations require transparent data handling and participant consent |
| Technology enhances protection | Encryption and multi-factor authentication safeguard scheduling information from breaches |
| Privacy-first methods accelerate planning | Research shows 40% time savings in multi-day event coordination |
Understanding Privacy in Multi-Day Group Scheduling
Participant availability data reveals far more than simple time slots. When you collect detailed schedules, you're gathering information about personal routines, work commitments, family obligations, and lifestyle patterns. Conventional scheduling tools expose detailed participant availability patterns, risking privacy breaches and unwanted inferences about personal life.
Traditional platforms rarely implement adequate safeguards for this sensitive information. The data sits vulnerable to breaches, misuse, or unintended disclosure to other participants. For multi-day events with larger groups, these risks multiply exponentially.
The consequences extend beyond data security. Privacy concerns directly impact scheduling efficiency by making participants reluctant to share complete availability information. This hesitation triggers endless back-and-forth communication rounds, delaying your event planning process significantly. Understanding these scheduling trends in 2025 helps coordinators recognize why privacy protection matters for speed.
Consider what availability data can reveal:
- Regular weekday blocks suggesting specific work schedules or childcare responsibilities
- Weekend patterns indicating personal commitments or hobbies
- Consistent time slots revealing religious observances or therapy appointments
- Travel windows exposing vacation plans or business trips
- Combined patterns allowing re-identification even in supposedly anonymous systems
Protecting this information isn't just ethical, it's strategic. When participants trust your scheduling process, they respond faster and more honestly, accelerating your entire coordination workflow. Implementing group calendar tips that prioritize privacy transforms hesitant participants into engaged collaborators.
Common Privacy Risks in Traditional Scheduling Tools
Most event coordinators use scheduling platforms without realizing the privacy vulnerabilities built into their design. These tools typically require participants to share comprehensive availability grids, creating detailed digital profiles of personal schedules. Sophisticated analysis can re-identify individuals even when systems claim anonymity.
The indirect inferences pose the greatest threat. Someone reviewing availability patterns might deduce participants' work situations, family structures, or personal habits. These revelations create discomfort that manifests as delayed responses or incomplete information sharing.
Privacy concerns slow down scheduling when participants fear oversharing or misuse of their availability data leading to lower participation rates.
Privacy concerns slow down scheduling when participants fear oversharing or misuse of their availability data leading to lower participation rates.
This hesitation cascades into operational problems for coordinators. Lower willingness to share availability promptly means more follow-up emails, additional reminder messages, and extended planning timelines. What should take days stretches into weeks.
The trust deficit becomes self-reinforcing. Each scheduling round that exposes personal patterns makes participants more cautious in future events. Your reputation as a coordinator suffers when people associate your events with privacy concerns.
Common vulnerabilities include:
- Public visibility of individual availability submissions to all participants
- Permanent storage of detailed schedule data without clear retention policies
- Lack of encryption protecting data during transmission or storage
- No authentication requirements allowing unauthorized access to scheduling pages
- Inadequate consent mechanisms for data collection and usage
Addressing these risks isn't optional for effective coordination. Creating an efficient scheduling workflow requires acknowledging that privacy protection and planning speed work together, not against each other. When participants feel safe, they cooperate faster.
Inverse Scheduling: A Privacy-First Approach
Inverse scheduling flips traditional coordination on its head. Instead of asking when participants are available, this method requests only their unavailable dates. This simple reversal fundamentally changes the privacy equation.
The approach minimizes sensitive data exposure by shifting what information gets shared. Marking busy times reveals far less about personal life than detailing free availability. You're no longer broadcasting your open schedule for analysis.
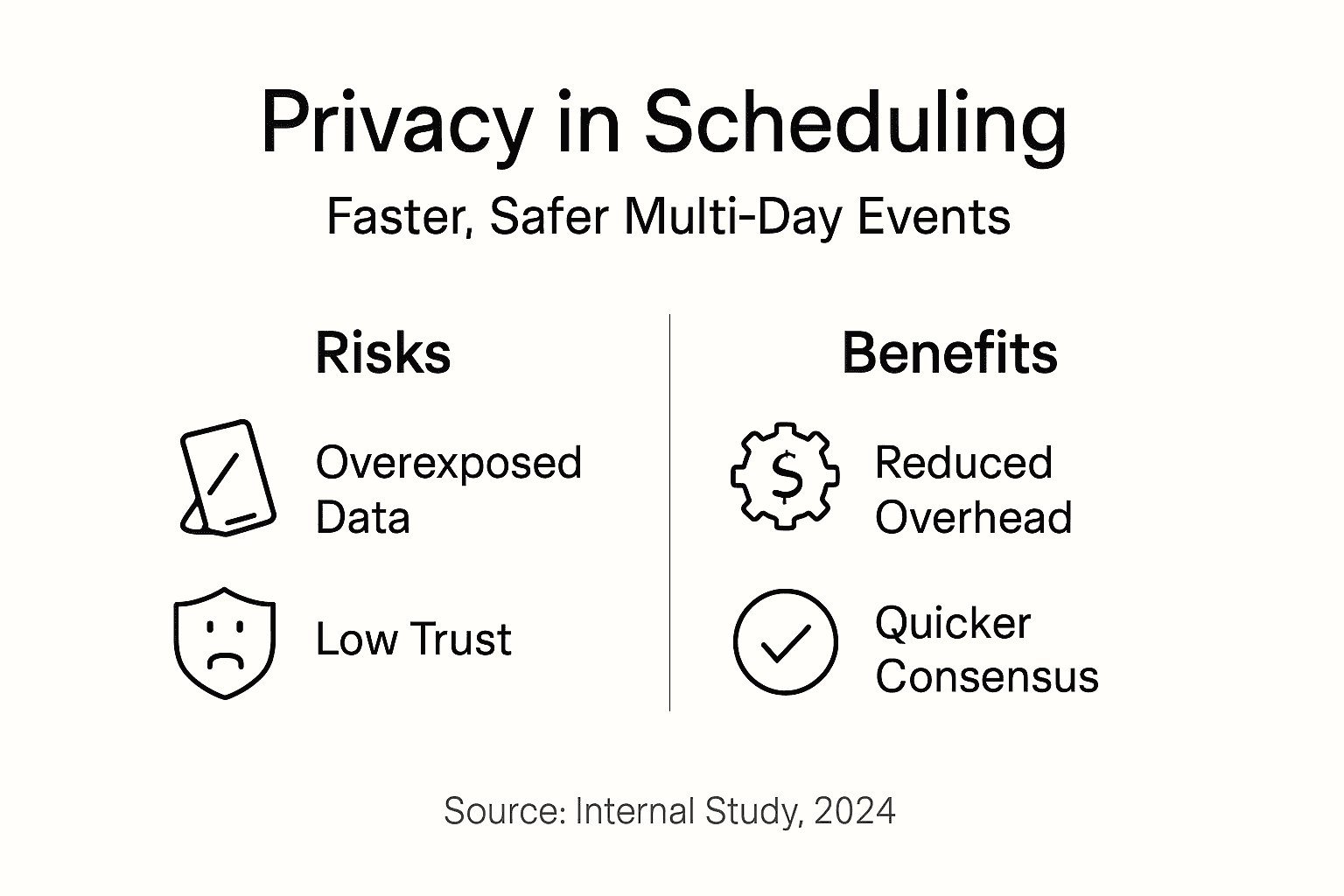
Research demonstrates that inverse scheduling reduces sensitive data exposure and saves up to 40% scheduling time for multi-day events. Participants complete submissions faster because marking a few busy days takes less cognitive effort than calculating and entering all available time slots.

The method also accelerates consensus building. With traditional polling, coordinators must analyze overlapping availability across numerous participants. Inverse scheduling simplifies this by highlighting conflicts immediately, making optimal dates obvious at a glance.
| Metric | Traditional Availability Polling | Inverse Scheduling |
|---|---|---|
| Data Exposure | Complete free time patterns | Limited busy dates only |
| Participant Completion Time | 5-8 minutes average | 2-3 minutes average |
| Privacy Protection | Low (reveals personal routines) | High (minimal pattern disclosure) |
| Consensus Speed | Multiple communication rounds | Single submission round typical |
| Participant Hesitation | Common due to oversharing concerns | Reduced with limited data sharing |
Implementing inverse scheduling for your multi-day events:
- Define your event date range broadly to accommodate participant constraints
- Create a scheduling interface where participants mark unavailable dates only
- Ensure the system displays aggregate conflicts without revealing individual submissions
- Identify dates with zero or minimal conflicts as optimal event windows
- Confirm the selected date and communicate the decision transparently
- Delete unnecessary scheduling data after event confirmation
This workflow naturally optimizes event scheduling by reducing both privacy risks and coordination overhead simultaneously.
Pro tip: When introducing inverse scheduling to your group, explicitly explain how it protects their privacy while speeding planning. This transparency increases participation rates and submission speed because people understand the dual benefits they're receiving.
Privacy Compliance and Regulatory Considerations
Regulations like GDPR mandate strict requirements for collecting, storing, and processing personal data, including availability information. Event coordinators bear legal responsibility for ensuring their scheduling practices comply with applicable privacy laws.
GDPR requires explicit participant consent before collecting availability data. You must clearly communicate what information you're gathering, how you'll use it, how long you'll retain it, and who can access it. Vague privacy notices don't satisfy these requirements.
Transparency builds trust while ensuring compliance. When participants understand your data handling practices, they feel more comfortable sharing necessary scheduling information. This trust accelerates responses and improves data quality.
Non-compliance carries serious consequences:
- Financial penalties reaching millions of euros depending on violation severity
- Legal liability for data breaches affecting participant information
- Reputational damage harming your ability to organize future events
- Loss of participant trust making coordination increasingly difficult
- Potential personal liability for coordinators in certain jurisdictions
Privacy-first scheduling methods naturally support compliance by minimizing data collection. When your process requests only essential information and implements decentralized scheduling approaches, you reduce regulatory exposure while improving efficiency. Less data collected means less data to secure, retain, and potentially breach.
Compliance isn't just about avoiding penalties. Meeting privacy requirements demonstrates professionalism and respect for participants. These qualities distinguish exceptional coordinators from adequate ones, building your reputation and making future event planning smoother.
Technical Solutions for Enhancing Scheduling Privacy
Modern scheduling platforms implement multiple technical safeguards to protect participant data. Understanding these technologies helps coordinators evaluate tools and make informed choices.
TLS encryption protects data during transmission between participants and scheduling servers. This prevents interception by unauthorized parties monitoring network traffic. Any platform handling sensitive scheduling information should implement HTTPS as a baseline security measure.
Multi-factor authentication adds a crucial security layer by requiring additional verification beyond passwords. This prevents unauthorized access even when login credentials are compromised. For coordination involving sensitive events, MFA becomes essential.
Privacy-friendly scheduling platforms that reveal only aggregate availability data improve security without sacrificing scheduling efficiency. These systems use algorithms that compute optimal dates without exposing individual availability patterns to coordinators or other participants.
Advanced cryptographic methods take protection further:
- Homomorphic encryption enabling computation on encrypted data without decryption
- Secure multi-party computation allowing collaborative scheduling without revealing individual inputs
- Zero-knowledge proofs verifying availability constraints without exposing actual schedules
- Differential privacy adding mathematical noise to prevent re-identification while preserving utility
While these advanced techniques may sound complex, their implementation is invisible to users. Participants simply submit their constraints while the underlying technology maintains privacy guarantees automatically.
Choosing platforms with robust technical safeguards reduces breach risks and builds participant confidence. When evaluating scheduling tools for your multi-day event tips, prioritize those demonstrating clear commitments to data security through transparent technical implementations.
Practical Advice for Event Coordinators to Safeguard Privacy
Protecting participant privacy requires intentional planning and ongoing vigilance. These actionable steps help coordinators build privacy protection into their scheduling workflow.
Start by conducting comprehensive privacy risk assessments before each event. Event planners should perform comprehensive risk assessments including privacy considerations to build safer, more trusted multi-day events. Identify what data you truly need versus what's merely convenient to collect.
Tool selection matters enormously. Prioritize platforms supporting inverse scheduling, strong encryption, and minimal data retention. Free tools aren't always privacy-friendly, while some paid platforms still implement poor security practices. Evaluate based on technical capabilities, not price.
Clear communication builds trust and ensures informed participation. Create simple privacy notices explaining your data handling practices in plain language. Avoid legal jargon that obscures rather than clarifies your intentions.
Implementing privacy-focused coordination:
- Assess privacy risks specific to your event type and participant demographics
- Select scheduling tools with demonstrated privacy and security features
- Draft clear, accessible privacy notices for participant review
- Obtain explicit consent before collecting any availability information
- Implement access controls limiting who can view scheduling data
- Establish data retention policies and delete information promptly after events
- Monitor platform settings regularly to prevent inadvertent exposure
- Stay informed about evolving privacy regulations affecting your jurisdiction
Maintaining inclusive scheduling practices requires recognizing that privacy protection affects all participants equally. Some may have particularly sensitive scheduling needs related to personal safety, employment situations, or family circumstances. Your privacy practices should accommodate these varied requirements without requiring explanations.
Pro tip: Schedule quarterly reviews of your scheduling tool settings and privacy practices. Platforms update features regularly, sometimes changing default privacy configurations. Regular audits prevent unintentional data exposure as systems evolve.
Common Misconceptions About Privacy in Scheduling
Several widespread myths prevent coordinators from adopting privacy-enhanced scheduling methods. Correcting these misunderstandings supports informed decision-making.
Myth: Open-source scheduling software is inherently less secure because anyone can examine the code. Fact: Openness enables community security audits that identify and fix vulnerabilities faster than closed systems. Transparency in code review strengthens rather than weakens security.
Myth: Traditional scheduling platforms adequately protect participant privacy by default. Fact: Most conventional tools expose detailed availability patterns to coordinators and sometimes other participants, creating significant privacy risks that default settings don't address.
Myth: Efficient scheduling requires comprehensive data collection even if privacy suffers. Fact: Privacy-enhanced methods like inverse scheduling achieve faster consensus with less data exposure, proving efficiency and privacy work together.
Myth: Privacy protection adds complexity that participants won't tolerate. Fact: Well-designed privacy-first systems simplify the participant experience by requesting less information and streamlining submissions.
Key clarifications:
- Privacy protection speeds rather than slows scheduling when implemented correctly
- Participants respond more quickly and honestly when privacy concerns are addressed
- Regulatory compliance protects coordinators from legal liability while building trust
- Technical privacy safeguards operate invisibly without adding user friction
- Privacy-first tools often cost no more than conventional alternatives
Understanding these realities empowers coordinators to make choices based on facts rather than assumptions. Privacy-enhanced scheduling isn't a tradeoff against efficiency, it's a strategy that improves both outcomes simultaneously.
Summary and Bridging Privacy to Efficient Multi-Day Event Scheduling
Privacy protection forms the foundation of effective multi-day event coordination. When participants trust your data handling practices, they share availability information quickly and accurately, collapsing scheduling timelines dramatically.
Minimizing availability data exposure through methods like inverse scheduling removes the hesitation that causes delayed responses. Participants no longer worry about revealing too much personal information, so they complete submissions immediately rather than procrastinating.
Combining privacy-first approaches with technical safeguards delivers measurable efficiency gains:
- Faster participant response rates reducing coordination time by 40% or more
- Higher data quality as participants share accurate rather than cautious information
- Reduced communication overhead eliminating follow-up reminders and clarifications
- Improved participant satisfaction increasing willingness for future event participation
- Legal compliance protecting coordinators from regulatory penalties and liability
Adopting privacy as a foundational scheduling principle transforms your effectiveness as a coordinator. Your events gain reputations for respecting participants, making recruitment easier and response rates higher. The multi-day event planning best practices that separate exceptional coordinators from average ones increasingly center on privacy protection.
Privacy isn't an obstacle to overcome in event planning. It's a strategic advantage that accelerates your entire workflow while building the trust necessary for smooth coordination. Coordinators who recognize this reality gain significant competitive advantages in efficiency and participant satisfaction.
Explore Privacy-First Scheduling Tools for Your Next Event
WhenNOT implements inverse scheduling specifically designed for privacy-conscious event coordinators. Participants mark only their unavailable dates, protecting personal schedule patterns while accelerating consensus for multi-day events.
The platform requires no participant signups, eliminating another privacy friction point that delays responses. Creating events takes seconds, and sharing via simple links removes coordination barriers. Understanding why online scheduling tools enhance efficiency helps you appreciate how privacy-first design accelerates rather than hinders planning. Compare best group scheduling tools to see how inverse scheduling transforms coordination, then explore comprehensive multi-day event planning strategies that leverage privacy for speed.
FAQ
What is the main privacy risk when using traditional scheduling tools?
Traditional platforms expose detailed availability patterns revealing personal routines, work schedules, and lifestyle information. This data can enable unwanted inferences about participants' lives or even re-identification in supposedly anonymous systems.
How does inverse scheduling protect participant privacy?
Inverse scheduling requests only unavailable dates rather than complete availability schedules. This fundamental shift minimizes sensitive data exposure while actually speeding consensus by simplifying submissions and making conflicts immediately obvious.
Are scheduling platforms required to comply with GDPR?
Yes, any platform collecting personal availability data from EU participants must comply with GDPR requirements. Coordinators must ensure transparent data handling, obtain explicit consent, and implement appropriate security measures regardless of the tool they choose.
Can privacy-friendly scheduling tools still provide fast event coordination?
Absolutely. Privacy-enhanced methods like inverse scheduling reduce communication overhead by approximately 40% compared to traditional approaches. Protecting privacy actually accelerates coordination by increasing participant willingness to respond quickly and accurately.
What practical steps should event coordinators take to safeguard privacy?
Conduct privacy risk assessments before each event and select tools with strong security features like encryption and minimal data collection. Communicate your privacy practices clearly to participants, obtain informed consent, and regularly audit your tool settings to prevent inadvertent exposure.
